Receiving a call from a private or blocked number can trigger curiosity, concern, or even anxiety. Is it a long-lost friend? A job offer? Or something more troubling—like harassment or scam attempts? While the urge to uncover the identity behind a hidden caller is natural, doing so must be balanced with respect for privacy and adherence to the law. Fortunately, there are several effective, ethical, and legal strategies available to help you trace or manage unknown calls without overstepping boundaries.
Understanding Private and Blocked Numbers
When a caller uses a private, blocked, or restricted number, their phone number is intentionally hidden from your device’s display. This is often done through carrier-level services like *67 (in North America) or settings within smartphones that suppress outgoing ID. While legitimate users may block their number for privacy, scammers and telemarketers frequently exploit this feature to avoid accountability.
It's important to recognize that while you cannot always reveal the identity of every private caller, you can take proactive steps to assess risk, reduce unwanted contact, and protect yourself from potential threats—all within legal boundaries.
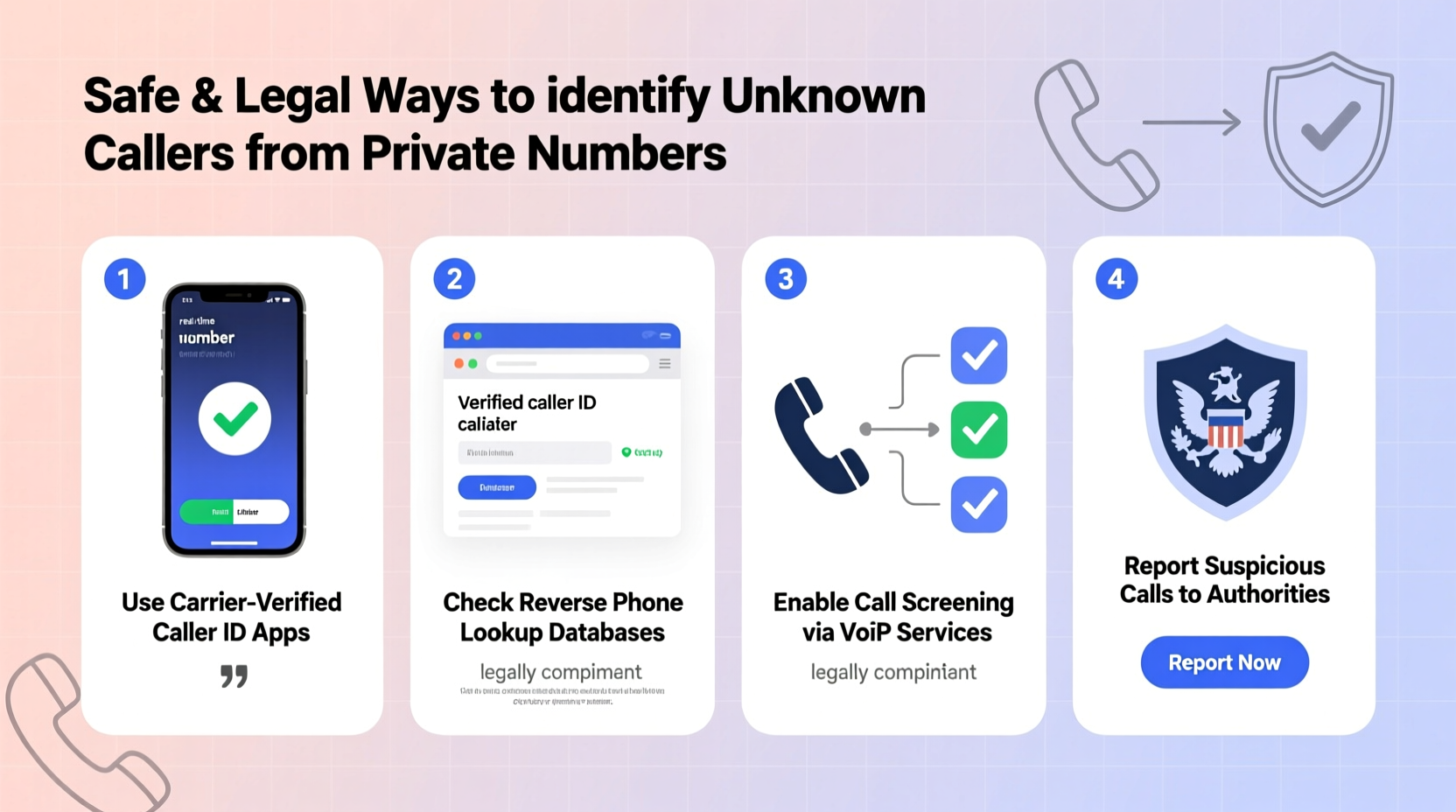
Legal Methods to Identify Unknown Callers
The key to safely identifying private callers lies in using tools and techniques that comply with telecommunications regulations such as the U.S. Telephone Consumer Protection Act (TCPA) and similar laws globally. Here are some proven, lawful approaches:
- Use Carrier Call-Blocking and Identification Services: Most major carriers now offer free or premium features that detect spam, label suspicious numbers, and provide reverse lookup capabilities. For example, AT&T Call Protect, T-Mobile Scam Shield, and Verizon Call Filter analyze call patterns and flag potentially harmful contacts.
- Enable Built-in Phone Features: Modern smartphones come with native anti-spam detection. iPhones use Silence Unknown Callers; Android devices offer Spam Protection in the Phone app. These features automatically divert unrecognized numbers to voicemail or warn you before answering.
- Leverage Third-Party Caller ID Apps: Applications like Truecaller, Hiya, and Whoscall maintain vast databases of reported numbers. When a private number has called others before, these apps may still provide context—even if the number itself remains hidden—based on user reports and behavior analysis.
- Request Caller Identification from Your Provider: Some telecom providers allow subscribers to activate Calling Number Delivery (CND) or Calling Line Identification (CLI), which ensures you receive caller info unless explicitly blocked by the sender. You can also ask about Anonymous Call Rejection—a service that prevents calls from private numbers altogether.
- Check Voicemail Messages Carefully: Even if the number is hidden, the caller might leave a message revealing clues—names, company details, background sounds, or callback instructions. Listen closely and document any useful information.
Step-by-Step Guide: Responding to a Suspicious Private Call
If you receive an unexpected call from a private number and suspect foul play, follow this structured approach:
- Do Not Answer Immediately: Let the call go to voicemail if possible. Legitimate callers typically leave messages; scammers rarely do.
- Assess the Voicemail (If Left): Note tone, language, urgency, and any identifying details. Avoid calling back unless you can verify the source independently.
- Search Online Using Context Clues: If the caller mentions a business, location, or individual, search those terms along with “scam” or “complaint.” Forums like Reddit or the Better Business Bureau may have relevant reports.
- Report to Authorities if Threatening: In cases involving threats, harassment, or fraud, file a report with the Federal Trade Commission (FTC), FCC, or local police. Provide call logs and recordings if available.
- Block Future Attempts: Use your phone or carrier tools to block future calls from that line, even if unidentified.
“While technology empowers us to screen calls, consumers must remain cautious. No tool guarantees 100% accuracy, and personal safety should always come first.” — Lisa Chen, Senior Telecommunications Analyst at the FCC
What Not to Do: Common Pitfalls
Some online methods promise instant identification of private numbers but operate in legal gray areas—or outright violate privacy laws. Avoid these risky actions:
| Action | Risk | Legal Status |
|---|---|---|
| Paying for \"private number unblocking\" services | Fraudulent claims, data theft | Often illegal or deceptive |
| Using spoofed return calls to trick caller ID | Violates telecom regulations | Prohibited under TCPA |
| Hiring unauthorized tracing agencies | Privacy violations, misuse of data | Unregulated and potentially criminal |
| Sharing private numbers publicly online | Defamation, harassment liability | Civil and criminal consequences |
Real Example: Handling Persistent Harassment Calls
Sarah, a small business owner in Oregon, began receiving daily calls from a private number. The caller never spoke, but the repeated ringing disrupted her work. She initially ignored them, but after two weeks, she decided to act.
First, she enabled Anonymous Call Rejection through her provider, which stopped most calls. One slipped through when the caller temporarily unblocked their number. Sarah let it ring to voicemail. Though no message was left, her phone logged the timestamp and noted the call lasted 17 seconds—consistent with automated dialing.
She then searched the approximate time and frequency pattern online and found a forum post describing identical behavior from a known robocall operation based in another state. Armed with this, she filed a complaint with the FTC and marked the number as spam in her carrier app. The calls ceased within days.
This case illustrates how combining technical tools with careful observation can resolve issues without invasive or unlawful measures.
Checklist: Safely Managing Private Number Calls
- ✅ Enable spam protection on your smartphone
- ✅ Activate Anonymous Call Rejection via your carrier
- ✅ Install a trusted caller ID app (e.g., Truecaller or Hiya)
- ✅ Do not return calls from unknown private numbers
- ✅ Document repeated or threatening calls (dates, times, patterns)
- ✅ Report harassment to the FTC at reportfraud.ftc.gov
- ✅ Educate family members, especially seniors, about scam red flags
Frequently Asked Questions
Can I legally find out who called me from a private number?
You cannot forcibly unmask a caller who has legally blocked their number. However, you can use indirect methods—like analyzing voicemails, leveraging caller ID apps, or reporting persistent abuse—to gain insight into the origin of the call, all within legal limits.
Are apps like Truecaller safe and legal to use?
Yes, when used responsibly. Truecaller and similar services rely on crowdsourced data and public directories. They do not hack or access private telecom records. However, be mindful of privacy concerns—some users object to having their numbers listed without explicit consent.
What should I do if a private number threatens me?
Immediately stop engaging. Save the call log, note the time and any audio (if recorded legally), and report the incident to law enforcement and the FCC. In urgent situations, contact local police. Threatening communications may constitute criminal harassment.
Conclusion: Stay Informed, Stay Protected
Dealing with private number calls doesn’t require aggressive tactics or questionable tools. By relying on verified technologies, understanding your rights, and responding thoughtfully, you can manage unknown callers effectively and ethically. The goal isn’t to invade privacy—but to protect your own.









 浙公网安备
33010002000092号
浙公网安备
33010002000092号 浙B2-20120091-4
浙B2-20120091-4
Comments
No comments yet. Why don't you start the discussion?